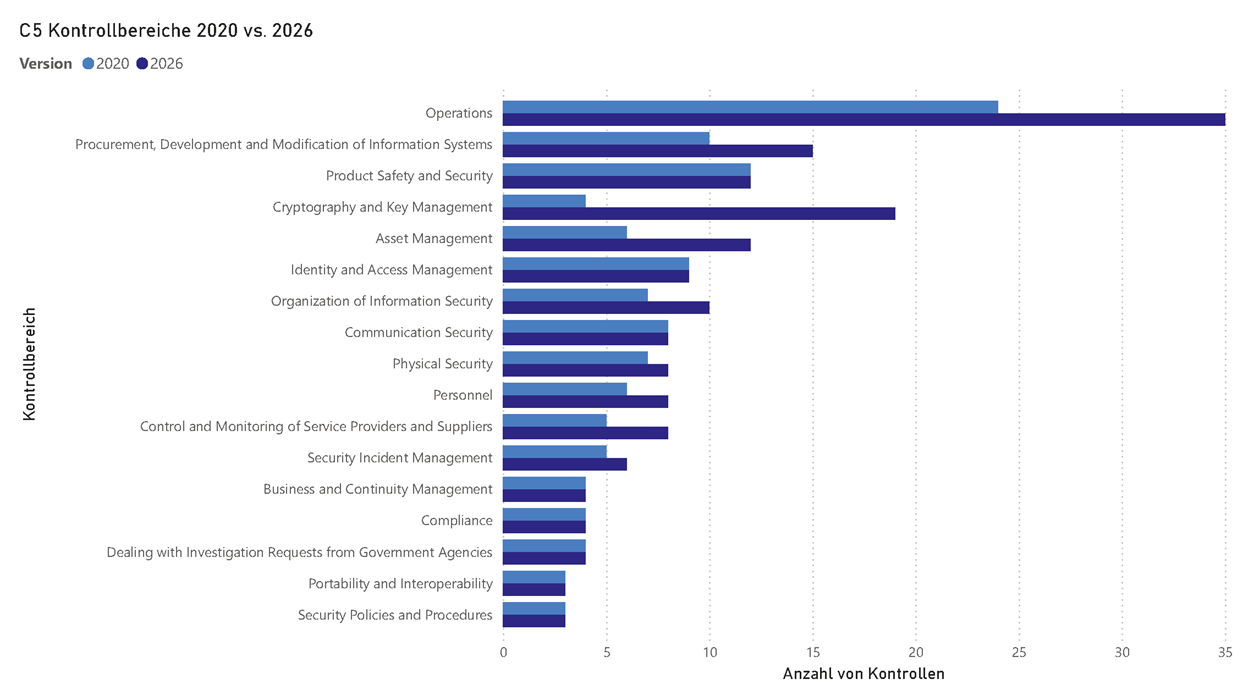
The final version of BSI C5:2026 has been published. The new version of the criteria catalogue replaces the current standard C5:2020. The German Federal Office for Information Security (BSI) is thus setting new standards for the assessment of cloud security. Compared to the 2020 version, the catalogue has been significantly expanded both in terms of content and structure.
The new requirements will become binding for assessment periods from 1 June 2027. Adoption of the new criteria is already permitted before the effective date. Early implementation is strongly recommended, especially for cloud providers that offer their services in regulated or security-critical markets.