Cyber incidents are no longer rare, isolated IT events. They are a fundamental business risk that can interrupt operations, erode trust, and trigger regulatory scrutiny. Leading organizations recognize that prevention alone is not enough—resilience is what determines whether the business survives and thrives under pressure.
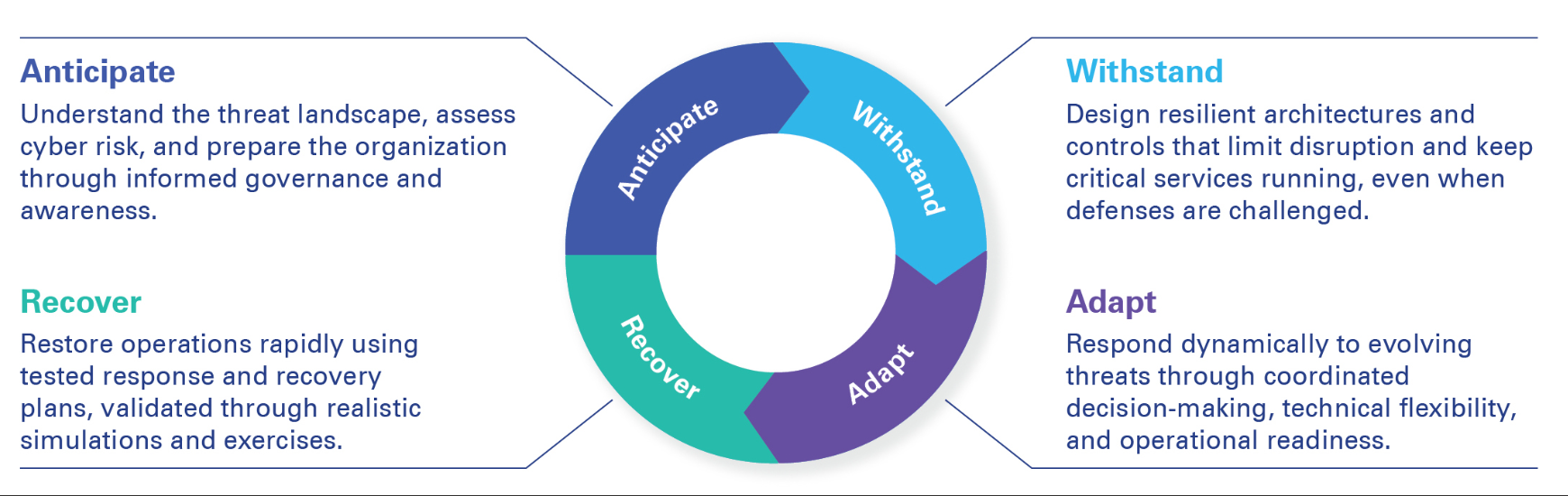
Cyber resilience is the ability to anticipate, withstand, adapt to, and recover from cyber incidents while maintaining critical business services. It moves organizations beyond fragmented security controls toward measurable operational continuity and executive confidence.